Remote Monitoring for Elevators | Secure Tools for improved Diagnostics
Many manufacturers offer a remote elevator monitoring option, which includes real-time system information such as car position, status, fault logs and more. This comes as no surprise with the maturation of the internet, cheap server space, and an increasing number of networked devices. Slowly, elevators and escalators are intersecting with the “Internet of Things” (IoT). I will stay away from the promises of IoT in this article. My objective is to:
1. Briefly introduce the concept and possibilities of remote monitoring and IoT in relation to elevators and escalators
2. Discuss the key features and benefits of KEB’s remote monitoring tools.
 IoT Fundamentals
IoT Fundamentals
What does IoT mean? How is this concept brought to life in elevators? In our world “Things” are the controller, door sensors, load weighers, power drive, etc. Before achieving networking capability using the internet, these devices must be connected at a lower level. Meaning there must be a common hardware (RS485, Ethernet, wireless) and software used by the remote monitoring system to communicate and collect system data. The next challenge is to connect the system to the internet for remote communication. Once this is complete, remote connections are possible and system information can be sent to elevator techs, design engineers, and decision makers instantaneously.
The possibilities to utilize this connection are virtually endless ranging from remote troubleshooting to faster shutdown response times. An example could be a high profile job with intermittent elevator shutdowns. The only clue is a generic “NO Drive ON” fault from the controller, and unfortunately, the drive has no faults in the log since the last shutdown. Now the game begins of replacing components one-by-one hoping the problem is resolved. All parties involved become increasingly frustrated. Now let’s say the system has a modern-day remote monitoring system and is monitoring the drive IO. When the system faults with a “NO Drive ON” fault a detailed log is emailed to the responsible elevator technician. The log proves the DRO Relay from the drive is actually picked during this fault but still the signal isn’t getting to the controller. The prints show the DRO relay is in series with a pilot relay. Now the technician can eliminate incorrect controller signaling, faulty drive, and look at the wiring and pilot relay between the DRO relay and controller. The connected system will reduce the time and money spent on troubleshooting and replacing other components with specific fault diagnostics relayed in real-time.
The ability to connect, collect, and analyze the data from an elevator or escalator benefits all stakeholders involved. Unfortunately, in practice, this isn’t as easy as it sounds. Finding compatible hardware and software is difficult, and collecting a mass of data without knowledge of how to analyze it is unhelpful. Most importantly, the system must be secure and the information on it must be private to the world. The implementation of a remote maintenance system requires careful planning and design. KEB offers help with secure remote connections to systems using VPN technology and data collection with COMBIVIS Connect™ and a line of Industrial Routers, HMIs and PLCs.
KEB’s Remote Access Solution
KEB’s C6 Router, HMI, and PLCs offer the possibility for remote connections as standard. Each of these products is equipped with the proper hardware to connect to systems with Ethernet and serial ports (RS232/422/485). Many suppliers offer compatible hardware; the differentiating technology between KEB’s solution and competitors is the COMBIVIS Connect architecture and COMBIVIS Studio HMI software.
The COMBIVIS Connect architecture is composed of three interconnected components: the control center (PC application), runtime (software on KEB hardware), and server infrastructure. Working together, a secure end-to-end connection between the control center and system network is generated via a virtual private network (VPN).
COMBIVIS Connect Architecture
The relationship between the control and runtime is a client-server type, where the control center is the client, and the runtime is the server. The KEB server infrastructure acts as an intermediary point to discover, reach, and authenticate connections. Using outbound connections to an access server the control center sends user credentials and a list of devices registered to the customer’s account. At the same time the runtime sends its availability with encrypted identification certificates with outbound connections. It is important to note that passwords are never stored in the control center or server databases. Instead, they are stored as an encrypted hash value, which must match the hash value stored on the access server. Additionally, all connections use SSL/TLS protocol for encrypted data transfer ensuring data confidentiality. When a user connects to a device all security credentials are exchanged and the access server routes traffic to a relay server which acts as a bridge and common point for data transfer. To eliminate bottlenecks and ensure reliable connections, KEB has relay servers located all over the world. The relay server is always selected by the access server based on load and proximity.
Finally, when a VPN connection has been established, the runtime serves an IP address within the same physical machine network to a virtual Ethernet adapter installed by the control center. Therefore the control center PC is a true member of the machine network and can access any devices on it as if it were physically connected to an Ethernet or serial cable. For example, if a C6 Router is connected to a remote PLC, the user running the control center can perform a device scan with the associated PLC software and connect to the PLC.
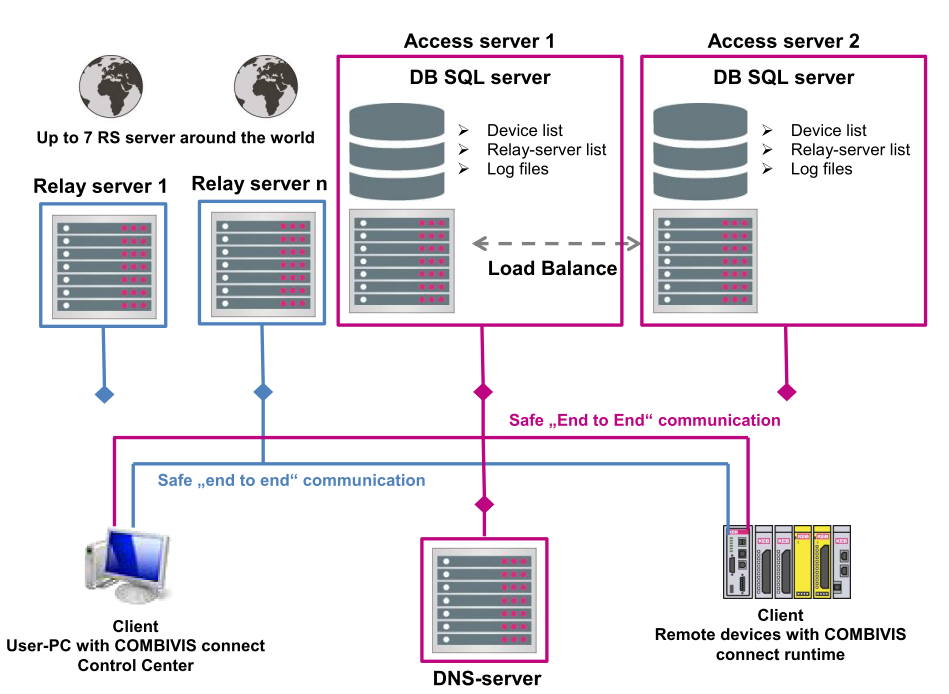
What is unique about this technology? Traditional VPN technology uses a central VPN server as an intermediary point between a VPN client and remote network. All data must pass through the central VPN server at all times. COMBIVIS Connect eliminates the need for a central VPN server and establishes a true virtual end-to-end connection, only using a relay server as an intermediary to route traffic. Not only is this more efficient but data traffic will never be seen or managed by KEB as even the traffic through the relay server is fully encrypted.
Security precautions don’t stop with VPN connections. KEB developed the COMBIVIS Connect architecture based on industrial cyber security standards ISA 99, and IEC 62442. COMBIVIS Connect’s architecture was proven to be secure and compliant with cyber security standards as it successfully passed an audit by an independent 3rd party German security organization Protect GmBH.
Control Center features
Luckily, the complexity of the secure connection mechanism utilized by COMBIVIS Connect is always hidden to the user. Management of the control center is user-friendly yet contains many features to ensure asset security.
The control center is the PC application used by the remote user, each of which will belong to a customer account called the “Domain”. Each domain can be organized in a hierarchy of folders, devices, users, groups, and firewall policies. Subfolders inherit users and firewalls of root folders but are completely private to other subfolders. This feature is very useful for managing a large number of devices. For example, a contractor can create folders for specific jobs or routes. They can then create users for the technicians responsible for each job or route in a specific folder. When each technician logs into the domain, they can only view devices within the folder they are given permission to access. KEB devices can also be viewed, configured, and accessed within the control center. Even before connecting to a remote network the control center uses several features to control and prevent unintended device connections with user management, firewall policies, and activity audits.
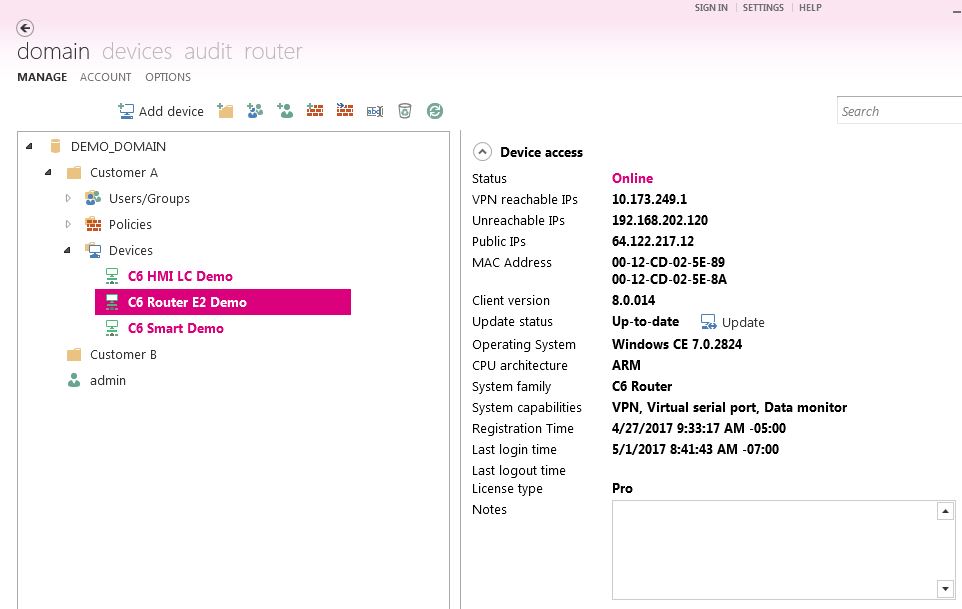
User management
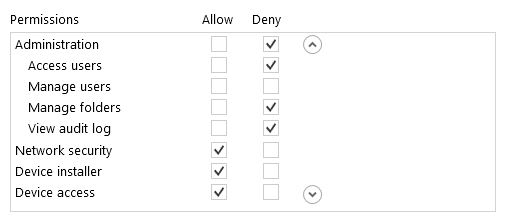
First, the domain account is private and can only be accessed by users with a username and password. Each domain account has an administrator that can manage all users and groups by defining special permission profiles for all users. Permission profiles define the rights for, domain administration, device installation, network security configuration (firewall policy creation), and device access. Device access rights can be further defined by limiting device actions such as remote network access, read remote files, write remote files etc. The domain administrator also has an option to track the activity of all users, and devices using an audit feature.
Audit
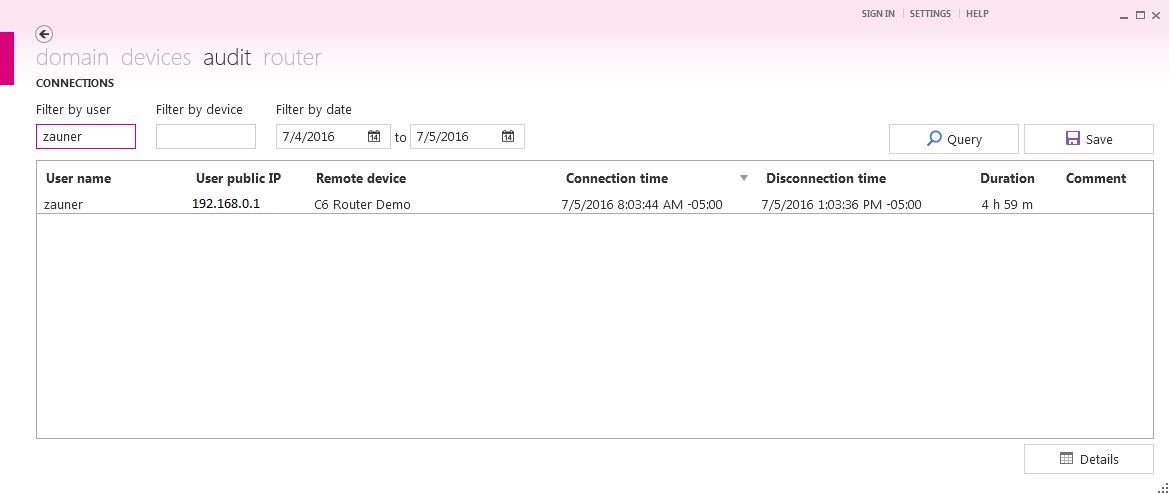
For complete visibility of all domain activity, the audit tool tracks all user and device interactions. This provides a complete record of who connected to what device, for how long, and what they did (VPN connect, transfer file, etc.). Additionally, a log on each device is kept with similar information.
Firewall policies
In addition to end to end-to-end VPN connections, traffic to and from each remote device can be further limited by the creation of firewall policies. Firewall policies can restrict traffic by MAC address , and Ethernet type. Depending on the Ethernet type further restrictions can be applied such as protocol, IP address and port. All policies can be defined as one-way or two-way which adds protection to the remote user’s network.
Data collection
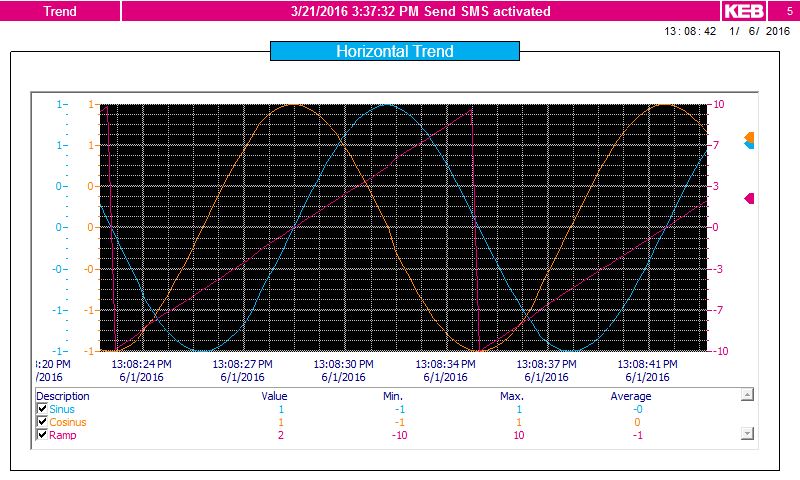
Remote monitoring systems become more powerful and useful with data collection. Data collection and visualization can be performed using KEB products with HMI runtime installed. COMBIVIS Studio HMI is the software tool utilized to develop HMI projects for data logging and visualizations. COMBIVIS Studio HMI includes over 40+ common software drivers to interface with a variety of systems including Modbus, BacNet, and OPC UA. This data can be logged continuously with configured data loggers. Data files can then be abstracted using the control center, or through scheduled emails from the device. It is also possible to push out data to cloud databases such as Microsoft Azure, or Amazon Web Services (AWS) using MQTT protocol for advanced analytics. Instant notification to faults and shutdowns is possible with configurable alarms. Alarms can be associated with specific variables to send out an SMS or E-mail to alert techs of faults. Lastly, real-time visualizations can be created and viewed. The control center offers remote viewing of HMI projects running on the desktop of the C6 Router or C6 HMI.
In conclusion, elevators and escalator systems can greatly benefit from remote monitoring systems. With many different options on the market today, careful planning should be taken when deciding to undertake such a development. Trusted and well tested tools should be utilized in such a system. KEB offers a wide range of proven hardware and software tools for integration into remote elevator monitoring systems.
Colin Zauner
Controls Application Engineer
This article originally appeared in Elevator World Magazine, January 2018.
Let's Work Together
Connect with us today to learn more about our industrial automation solutions—and how to commission them for your application.